How to Clear HSTS Settings in Chrome and Firefox
How to Clear HSTS Settings in Chrome and Firefox
Mozilla Firefox and Google Chrome both are most powerful web browser with latest security updates to make your data and information secure on the web. HSTS stand for HTTP Strict Transport Security which is a web security feature but if you want to disable it for certain websites you can do it. In this article we learn how to clear HSTS in Chrome and Firefox browser .
What is HSTS?
HTTP Strict Transport Security (HSTS) is a simple website security feature that forces web browsers or user agents to communicate with servers only through HTTPS connections. HSTS improves security and prevents man-in-the-middle attacks, downgrade attacks, and cookie-hijacking. In other words, it’s a web security policy mechanism that forces web browsers to interact with it only via secure HTTPS connections (and never HTTP).
Because servers are usually not connected directly to each other, they must pass their requests and responses through a series of network routers. These routers, located in-between servers, have complete access to requests sent via HTTP connections. Since the data is transferred as unencrypted plain text, the routers can act as a “man in the middle” and read or manipulate data in transit.
This can cause users to receive manipulated information or be directed to hostile servers used by attackers to steal information like passwords and credit card info. This kind of interception can go undetected since a compromised HTTP response looks the same as a genuine response.
The HSTS policy forces all responses to pass through HTTPS connections instead of plain text HTTP. This ensures that the entire channel is encrypted before any data is sent, making it impossible for attackers to read or modify the data in transit.
New Tricks for Defeating SSL in Practice
HSTS was originally created in response to a vulnerability that was introduced by Moxie Marlinspike in a 2009 BlackHat Federal talk titled “New Tricks for Defeating SSL in Practice.” The particular vulnerability that HSTS defends against is the one illustrated by Marlinspike’s SSLStrip tool.
Essentially the tool works by converting secure HTTPS connections back to unsecured HTTP ones. HSTS remedies this by communicating to the browser that an HTTPS connection should always be in place. HSTS can also help to prevent cookie-based login credentials from being stolen by common tools such as Firesheep.
Unfortunately, some HSTS settings can inadvertently cause browser errors. For instance, if you’re using Chrome, you might run into:

If you attempt to reach the same site on another browser and don’t run into the same issues, it could just be a problem with how the HSTS settings have affected your original browser. In that case you will need to clear them. Here’s how to clear HSTS settings on Google Chrome and Mozilla Firefox.
How to Clear Clear HSTS Settings on Chrome
1. Close all tabs in Chrome.
2. Type “chrome://net-internals/#hsts” into your address bar to access the Network Internals Page.

3. In the “Query Domain” field, type your domain name and click OK, this will check to see the HSTS settings for your domain.
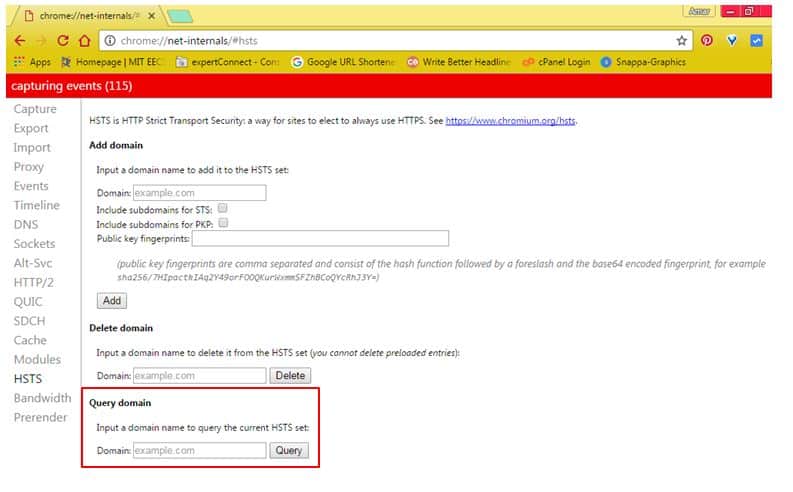
4. If HSTS is enable, type your domain name in the “Delete Domain” field and click OK.
5. Query your domain again, the results should say “not found.”
How to Clear Clear HSTS Settings on Firefox
1. Close all tabs in Firefox.
2. Open the Firefox “Browser Settings” and go to “History.”
3. Select “Show Complete History.”
4. Search for the domain you want to delete HSTS settings for, right click on it.
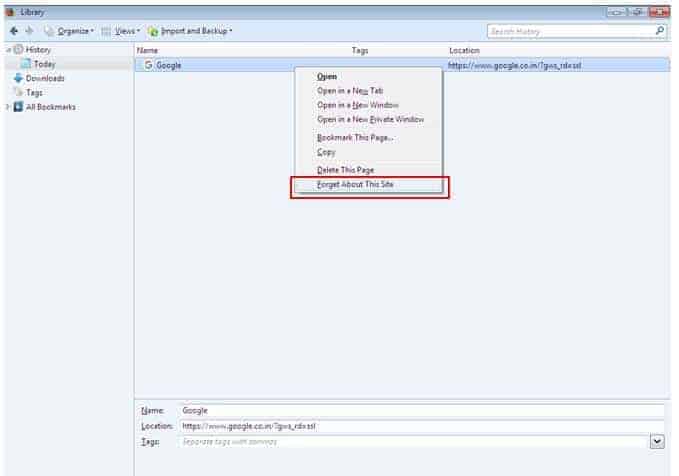
5. Choose “Forget About This Site.”
Alternative methods
If previous methods did not help, try these alternatives. To clear HSTS (HTTP Strict Transport Security) settings in Chrome and Firefox, you can follow the steps below:
Clearing HSTS Settings in Chrome:
- Open Google Chrome browser and type “chrome://net-internals/#hsts” in the address bar.
- Click on the “Delete domain security policies” button.
- Enter the domain name that you want to clear the HSTS settings for in the “Delete domain security policies” popup box, and then click on the “Delete” button.
- Restart your browser to ensure that the changes take effect.
Clearing HSTS Settings in Firefox:
- Open Firefox browser and type “about:config” in the address bar.
- Search for “security.enterprise_roots.enabled” and double-click on it to set its value to “false”.
- Search for “network.stricttransportsecurity.preloadlist” and double-click on it to set its value to “false”.
- Close the “about:config” tab and restart your browser to ensure that the changes take effect.
- To clear the HSTS settings for a specific domain, you can use the “Forget About This Site” feature. Simply right-click on the tab for the site you want to forget and select “Forget About This Site”. This will clear all cookies, history, and HSTS settings for that site.
Note: Clearing HSTS settings can make your browsing less secure. Only clear the HSTS settings if you are sure that it is safe to do so.
Final thoughts
HSTS setting is a good option for safe browsing but sometime it is not required , it is depend upon user requirement how to much security you want to browse internet over secure way.







